Facebook suffers from a URL redirection bug which never got patched even after responsible disclosure. But when they patch it they fail to give credit to the reporter. This bug has been reported by many hunters, and had gone to deaf ears. I am attaching few screenshots here of the bug which will give an insight to its impact on the Facebook users.
First reported on chat and patched without giving due credits:
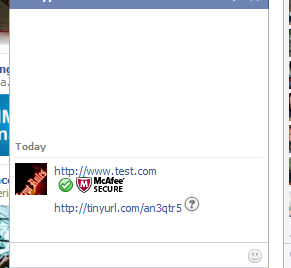
Attacker sends the URL to the victim. Right-click the link, and copy URL location reveals a intermediate facebook URL which redirects it to pass through the LinkShim.
Mask the URL with tinyURL or other URL shorting services. You can see the intermediate Facebook URL on the screenshot.
Replace the original URL with malicious URL, which may be an evil server.
A simple metasploit server in the backend, can help you gain a remote access to the victim’s PC.
Confirming remote access in the above screenshot.
Later this bug was found in the URL shared by users in an intermediate URL of the form https://www.facebook.com/l/<serviceURL>/Token
This is also their LinkShim feature. This was also patched without giving due credits.
Basically the screenshot below shows how the existing LinkShim works based on these examples.
I propose a modification to LinkShim which will prevent such redirects, 100%. But Facebook doesn’t seem to believe that 100% protection is possible. But, the below schematic diagram proposed by me works and blocks all kinds of redirects!
Many people reported this bug in various modules of Facebook and got a very poor response from the Facebook security team. They have a huge belief in their LinkShim algorithm, but, when testing it with special conditions it fails completely. The so called patch currently deployed is not optimization of their Algorithm but, stop redirecting pages via LinkShim. I cannot understand the logic here, when we can foresee a possible patch, the team was not even ready to discuss the issue.
Looking forward for comments from readers.
Cheers.